In right now’s cybersecurity panorama, it’s not nearly having sturdy defenses—it’s additionally about constructing belief and partnerships with the broader safety neighborhood. One easy however efficient option to display this openness is by implementing a safety.txt file. This small addition gives a transparent, standardized pathway for safety researchers to report vulnerabilities, lowering friction for many who wish to assist shield your group. Nevertheless, solely 4% of Fortune 500 firms presently use one, and that absence could possibly be sending the unsuitable message.
1. A Easy Step with Direct Advantages
The worth of a safety.txt file is rapid and tangible. It creates a single, accessible level of contact for safety researchers who could uncover vulnerabilities and have to report them rapidly. In a world the place threats evolve continually, the very last thing you need is for useful researchers to face hurdles in reaching your safety crew. This can be a low-cost, high-impact option to improve your responsiveness and streamline incident reporting.
Even when your organization doesn’t have a proper bug bounty program, a safety.txt file allows you to welcome and act on exterior safety disclosures. It’s about setting the best tone and exhibiting that your group values safety contributions from outdoors its partitions.
2. Balancing Disclosure Rewards: When and Easy methods to Talk
For firms that do supply rewards for disclosures, a safety.txt file can function a clear option to talk program particulars—or sign openness to the potential for a reward. In case your bug bounty program is public, embody it right here to offer researchers rapid readability on how they is perhaps compensated. But when your method is extra versatile, take into account a easy assertion like, “Contact for data on disclosure rewards,” which alerts a willingness to debate phrases with out committing to a inflexible construction.
This method allows you to talk curiosity with out limiting choices, permitting researchers to know that their contributions are appreciated, even when a structured reward isn’t outlined.
3. The Absence of Safety.txt: A Missed Alternative for Neighborhood Belief
Not having a safety.txt file is greater than a technical omission—it might sign a reluctance to have interaction with the safety neighborhood. By skipping this easy step, firms can unintentionally talk that they don’t worth the efforts of moral hackers, researchers, and white hats who might assist safe their programs. In a world the place collaboration is vital to a resilient safety posture, that’s a pricey message to ship.
That is very true as your group matures. For firms with well-developed safety postures (a cumulative rating of two.0 or above on frameworks like NIST or MITRE), the shortage of a safety.txt file turns into tougher to justify. As your safety capabilities develop, take into account how this minor addition can improve your status and replicate a dedication to open, constructive partnerships with the neighborhood.
Conclusion: Strengthening Safety By Openness and Belief
Adopting a safety.txt file isn’t nearly making a contact level; it’s a visual demonstration of your group’s perspective towards collaborative safety. If you create a transparent, open channel for vulnerability reporting, you’re reinforcing a message that moral researchers are welcome and valued. It’s an affordable option to foster belief, increase transparency, and align with finest practices in safety governance.
In case your group hasn’t but applied a safety.txt file, take into account the message this is perhaps sending. In a time the place belief is paramount, a small step like this may have outsized influence. Don’t let an oversight be mistaken for indifference—take the chance to sign your dedication to safety and neighborhood.
Contemplating including a safety.txt file or wish to discover extra methods to strengthen your safety program? Attain out—we’re right here to assist make safety finest practices accessible and actionable in your group.
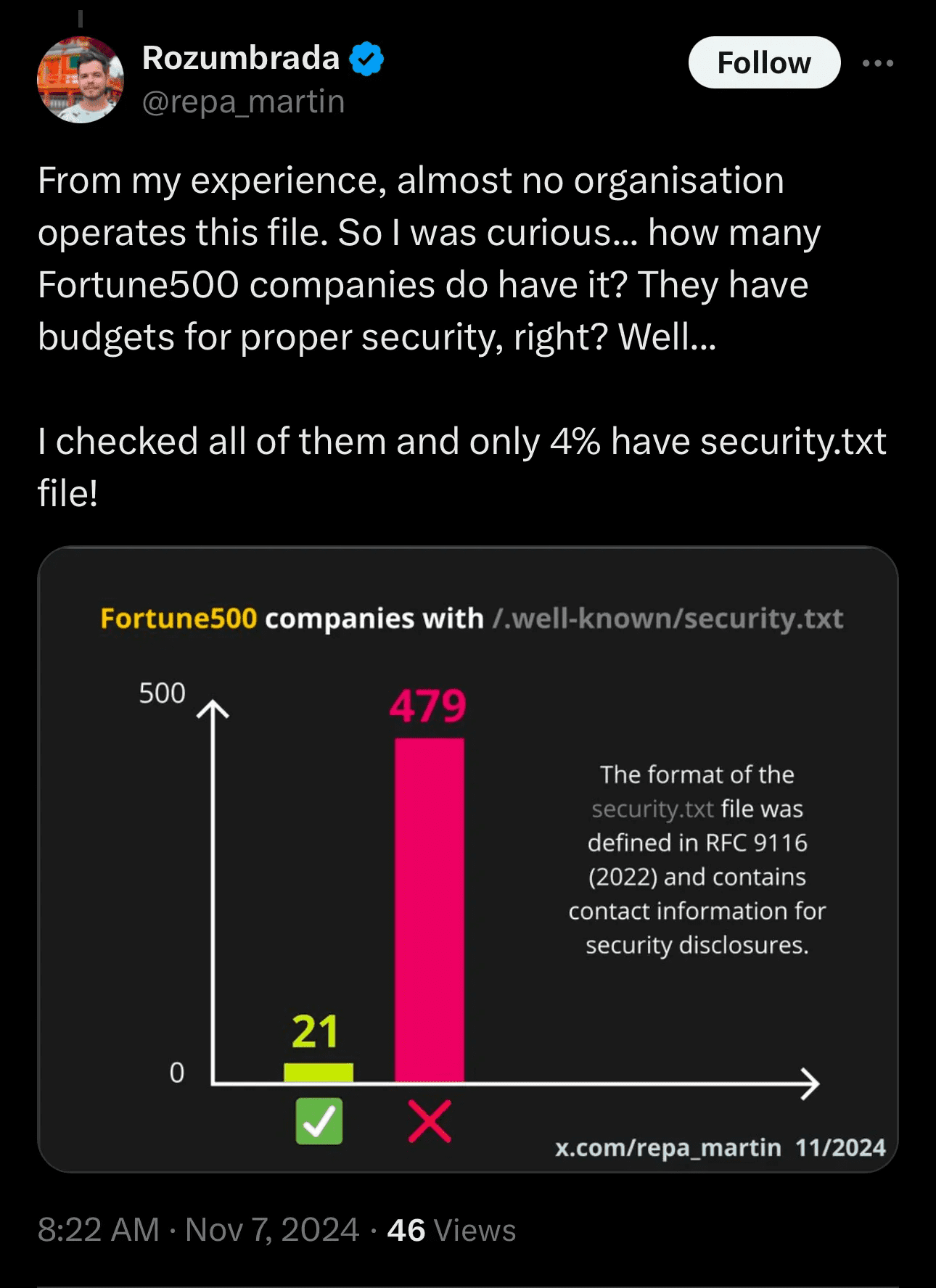
Determine 1. The Twitter Submit that Impressed this Weblog

